Backing up your data to a Linux based SFTP server is an inexpensive method that separates network shares (which can be attacked by crypto viruses) from your backups. You can configure Cloudberry’s SFTP backups with either password based access or with a shared cryptographic key so that regular passwords aren’t used. This document provides steps on using both methods to access an SFTP server with Cloudberry Backup.
SFTP advantages:
- Linux is easy to install.
- Doesn’t require advanced hardware.
- SFTP comes pre-configured with CentOS 7 server.
- Can easily be run on a cloud server, such as Digital Ocean or Linode.
- On systems with multiple mounted drives, you can specify the storage locations.
SFTP disadvantages:
- Not as fast as some other protocols, such as Minio
Pre-requisites:
- A Linux server such as ‘CentOS 7 Minimal’, which comes with SFTP pre-configured.
- To use Shared Key backups, you’ll need a copy of ‘Git Bash’ or similar environment on your Windows workstation. This allows you to create and manage shared key access with your Linux server.
Configuring Password Based SFTP Backups
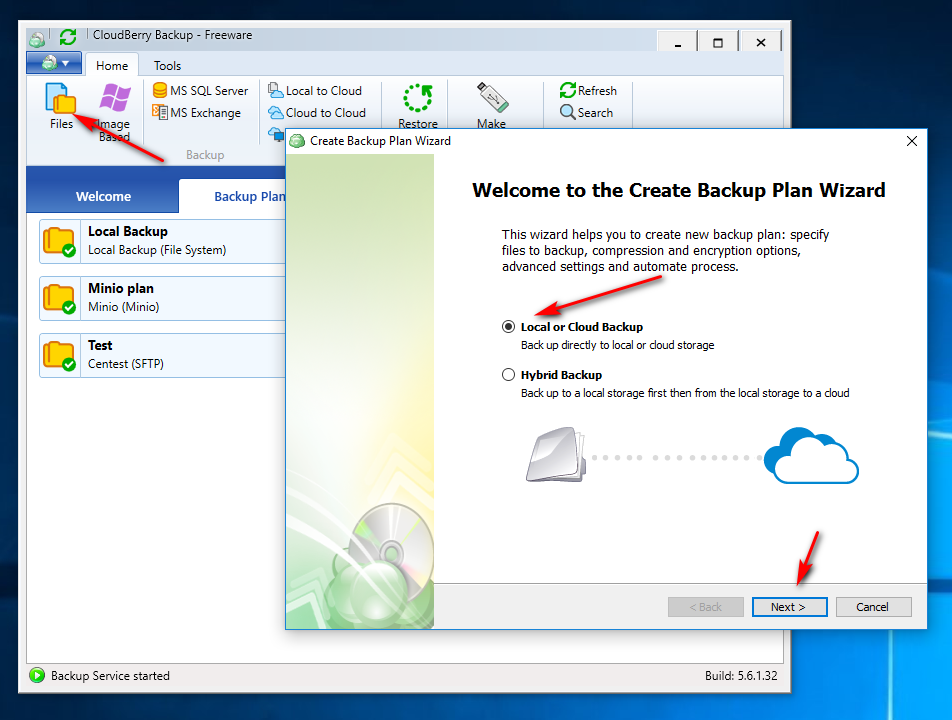
Launch Cloudberry Backup, click files in the upper-left corner, ensure ‘Local or Cloud Backup’ is selected and press ‘Next>’:
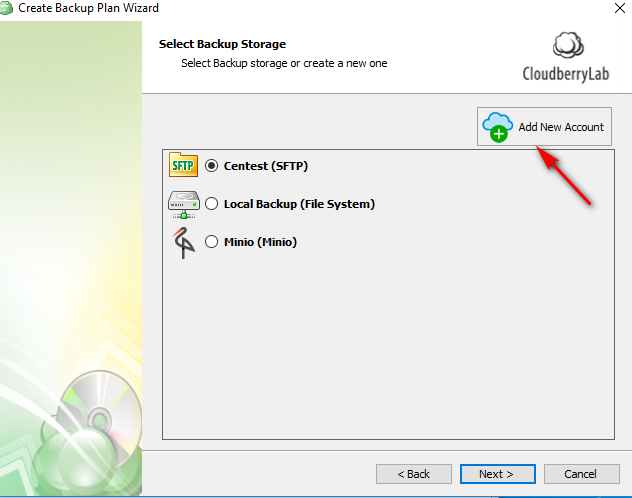
Select ‘Add New Account’:
Select ‘SFTP’ (on the left) and add your SFTP server information. Ensure you have previously created your ‘backups’ path and that your ‘backups’ account on the Linux server has full privileges to it:
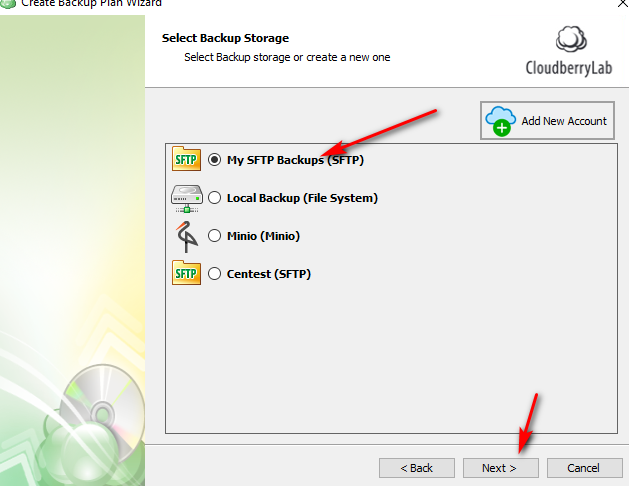
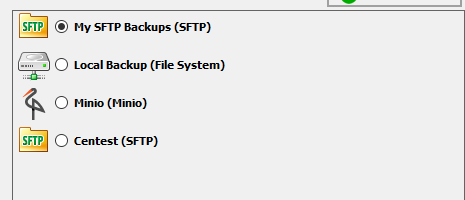
You should now be able to select your new Backup Storage account:
From here, you should be able to complete the rest of the Backup Wizard steps to create and customize your backup plan!
Configure Shared Key SFTP Backups
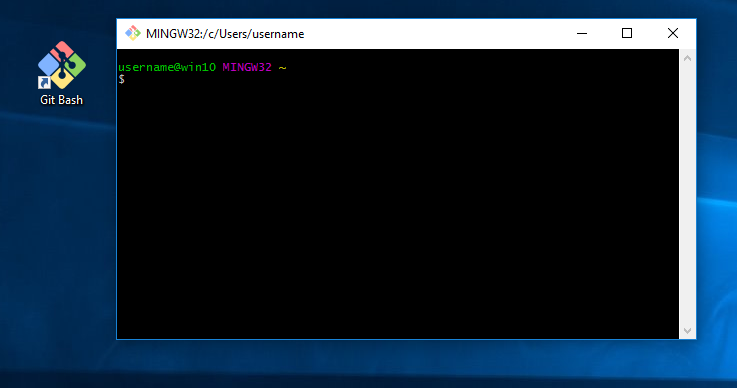
Prior to configuring Share Key SFTP backup in Cloudberry, install Git Bash onto your Windows workstation. Once installed, you should be able to click on the Git Bash icon and be presented with a Bash command line window.
Once you run Git Bash, you should be presented with:
Next, we’ll create our Windows based keys in Bash by running ssh-keygen and use the defaults until you’re back at the shell prompt:
Note: ssh-keygen creation has been simplified. Feel free to lookup best practices for this.
You should now have your private key in ~/.ssh/id_rsa as well as your public key in ~/.ssh/id_rsa.pub.
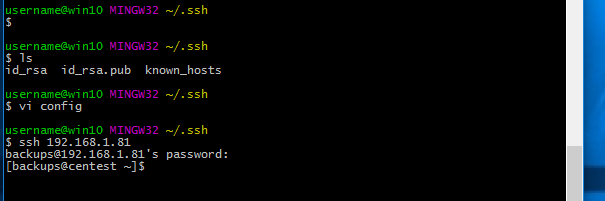
Next, let’s test our SSH access to the SFTP server. Since the username is different, we’ll need to add that:
When you’re asked to continue connecting, you will end up with a file called ‘~/.ssh/known_hosts‘. If you end up with errors, you may need to edit your known_hosts file and delete any previous related entries.
Optionally, you could add a ~/.ssh/config and add username and port parameters when accessing the server with SSH or SFTP.
Once you’ve saved the config file, you should now be able to run ssh without specifying the username. This is not used by Cloudberry, but is a nice feature for when you need to ssh into your server.
Now we’re ready to add our public key to the CentOS server for shared key access using the ‘ssh-copy-id‘ command in Git Bash:
This creates a file on the server called ‘/home/backups/.ssh/authorized_keys‘. If you end up with errors, you may need to edit your authorized_keys file and delete any previous related entries.
Note: This was performed in a test environment, and during that testing, I had to create and re-create the .ssh directories on both the Windows and CentOS systems. Be careful in a production environment.
Now that we’re able to login to the CentOS server using shared keys, we can configure Cloudberry for similar SFTP access.
In Cloudberry, create a new plan as before, however, you’ll need to selct the Private key authentication and to point to your private key file:
Note that you still need to enter the Port and Username in Cloudberry. If configured correctly, you should see the backup account listings page:
From there, you can continue as with password based SFTP backups.
Reference:
Downloads (as of June, 2017):
| CentOS 7 Minimal | http://isoredirect.centos.org/centos/7/isos/x86_64/CentOS-7-x86_64-Minimal-1611.iso |
| Git Bash (Windows) | https://git-scm.com/download/win |
| Cloudberry Free | https://www.cloudberrylab.com/blog/introducing-cloudberry-backup-freeware-version/ |







Comments are closed.